A The Nightmare: The Unguarded Gate
Let’s imagine the situation: a stranger (let’s call him the “Evil Hacker”) finds a free Ethernet cable on the side of the building that leads to an outdoor camera. He unscrews the camera, plugs in his laptop, and… BINGO! Since the switch port was open, he immediately gains access to the internal network.
What’s the solution? The “802.1X Team!”
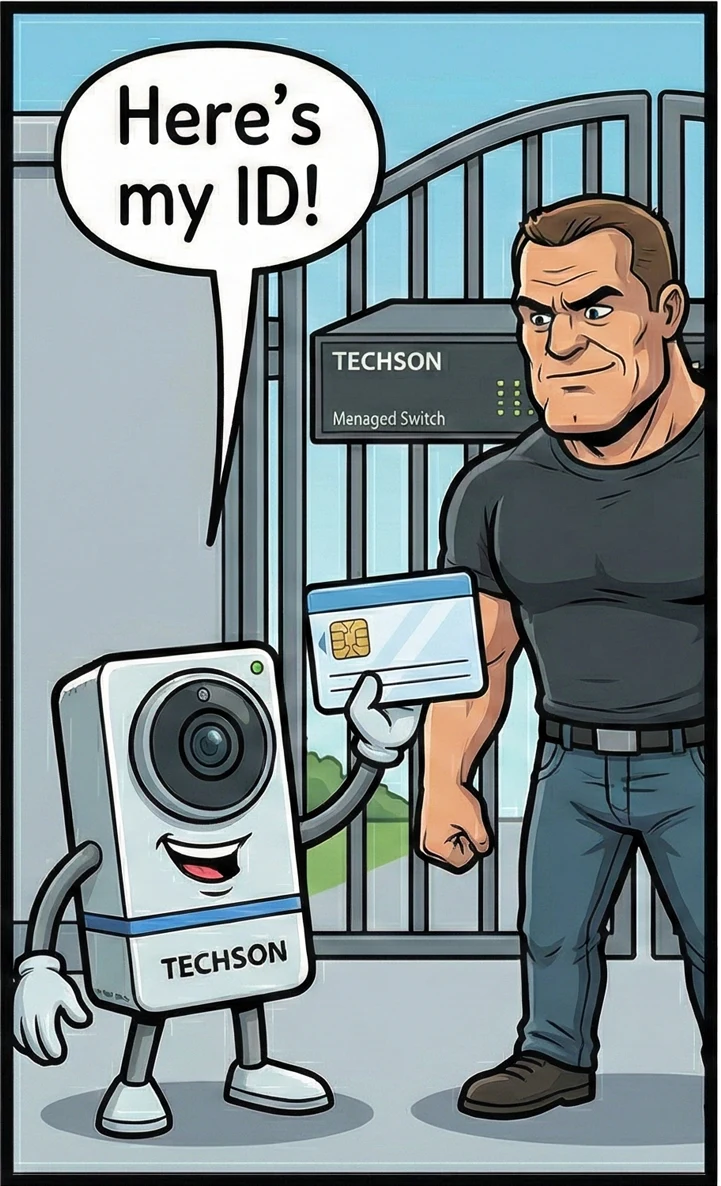
The solution is the 802.1X standard, which ties access to digital identities. Our system consists of three main players:
The Bouncer
He is the force. He physically locks the port and lets no one through without identification.
The Judge
Synology NAS
He is the knowledge. He holds the list of trusted devices and decides on access.
The Guest
It has an unforgeable digital ID (certificate) used to authenticate itself.

The Big Encounter (The Authentication Process)
When the camera is connected, a quick “conversation” takes place. The camera presents its ID to the switch. The switch, since it cannot read it, forwards it to the NAS. The NAS checks it against the “Judge’s list,” and if everything is in order, it responds to the switch: “GO AHEAD!”. Only then does the gate open.


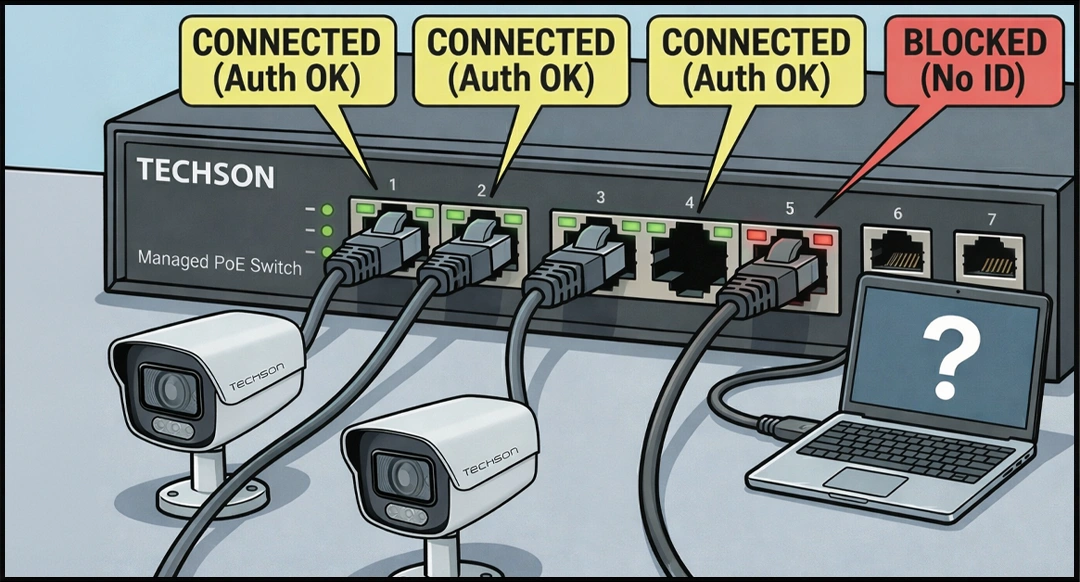
The Result: Green Light for the Good Guys, Wall for the Bad Guys
The system is visually clear during operation: on the front panel of the Techson Switch, the ports of authorized cameras light up green (“CONNECTED”), indicating successful access. However, if a hacker tries with a laptop, plugging in the cable won’t help. Without proper identification, the port does not allow traffic and remains closed (“BLOCKED”), the gate stays shut, and the network remains protected.